E-commerce sites utilizing Adobe’s Magento 2 software package are the goal of an ongoing marketing campaign that has been energetic given that at minimum January 2023.
The assaults, dubbed Xurum by Akamai, leverage a now-patched significant protection flaw (CVE-2022-24086, CVSS rating: 9.8) in Adobe Commerce and Magento Open up Resource that, if correctly exploited, could guide to arbitrary code execution.
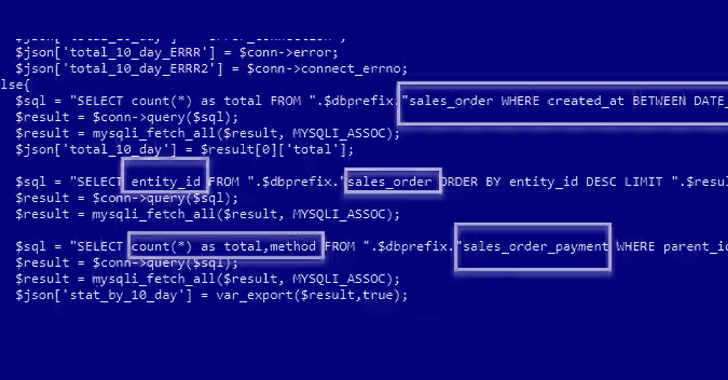
“The attacker looks to be intrigued in payment stats from the orders in the victim’s Magento keep positioned in the previous 10 days,” Akamai researchers reported in an investigation printed past week, attributing the marketing campaign to actors of Russian origin.
Some of the internet websites have also been noticed to be contaminated with very simple JavaScript-based skimmers that is intended to gather credit history card information and transmit it to a remote server. The precise scale of the marketing campaign continues to be unclear.

In the attack chains noticed by the business, CVE-2022-24086 is weaponized for initial obtain, subsequently exploiting the foothold to execute destructive PHP code that gathers information about the host and drops a internet shell named wso-ng that masquerades as a Google Procuring Ads part.
Not only is the internet shell backdoor run in memory, it also activated only when the attacker sends the cookie “magemojo000” in the HTTP request, after which facts about the product sales order payment strategies in the earlier 10 days is accessed and exfiltrated.
The attacks culminate with the development of a rogue admin person with the title “mageworx” (or “mageplaza”) in what appears to be a deliberate try to camouflage their actions as benign, for the two monikers refer to well-known Magento 2 extension stores.
wso-ng is stated to be an evolution of the WSO world wide web shell, incorporating a new hidden login webpage to steal credentials entered by victims. It even more integrates with respectable equipment like VirusTotal and SecurityTrails to glean the infected machine’s IP status and acquire specifics about other domains hosted on the same server.

Online shopping internet sites have been qualified for a long time by a course of attacks recognized as Magecart in which skimmer code is inserted into checkout internet pages with the objective of harvesting payment info entered by victims.
“The attackers have demonstrated a meticulous approach, focusing on unique Magento 2 circumstances somewhat than indiscriminately spraying their exploits across the world wide web,” the scientists reported.
“They display a superior stage of know-how in Magento and make investments substantial time in comprehending its internals, placing up attack infrastructure, and screening their exploits on authentic targets.”










More Stories
How Fairfield-based Knocking became CT’s fastest-growing startup
Amazon will start out tests drones for treatment deliveries
AI Briefing: Klarna hopes visual research in its e-commerce platform will assistance shoppers bridge in-man or woman, electronic hole