eCommerce servers are currently being targeted with distant accessibility malware that hides on Nginx servers in a way that makes it almost invisible to stability remedies.
The menace received the name NginRAT, a combination of the application it targets and the distant access capabilities it presents and is being employed in server-aspect assaults to steal payment card knowledge from on the internet suppliers.
NginRAT was identified on eCommerce servers in North America and Europe that had been infected with CronRAT, a distant access trojan (RAT) that hides payloads in tasks scheduled to execute on an invalid working day of the calendar.
NginRAT has contaminated servers in the U.S., Germany, and France wherever it injects into Nginx procedures that are indistinguishable from reputable ones, allowing for it to continue to be undetected.
RATs enable server-facet code modification
Scientists at safety business Sansec make clear that the new malware is sent CronRAT, despite the fact that equally of them fulfill the very same purpose: giving remote entry to the compromised system.
Willem de Groot, director of threat study at Sansec, instructed BleepingComputer that when employing really various techniques to keep their stealth, the two RATs appear to have the same position, acting as a backup for preserving remote entry.
Whoever is powering these strains of malware, is working with them to modify server-aspect code that authorized them to report knowledge submitted by customers (Write-up requests).
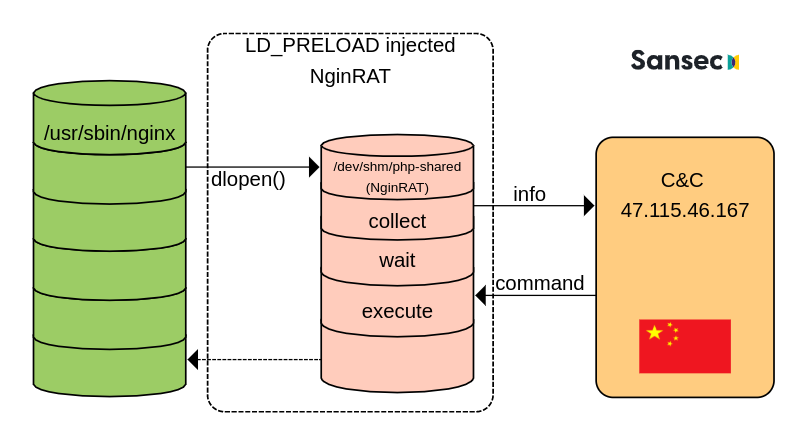
Sansec was equipped to study NginRAT right after creating a personalized CronRAT and observing the exchanges with the command and regulate server (C2) located in China.
The scientists tricked the C2 into sending and executing a rogue shared library payload, as part of the regular malicious conversation, disguising the NginRAT “more state-of-the-art piece of malware.”
“NginRAT fundamentally hijacks a host Nginx application to stay undetected. To do that, NginRAT modifies core operation of the Linux host program. When the authentic Nginx world-wide-web server works by using these operation (eg dlopen), NginRAT intercepts it to inject itself” – Sansec
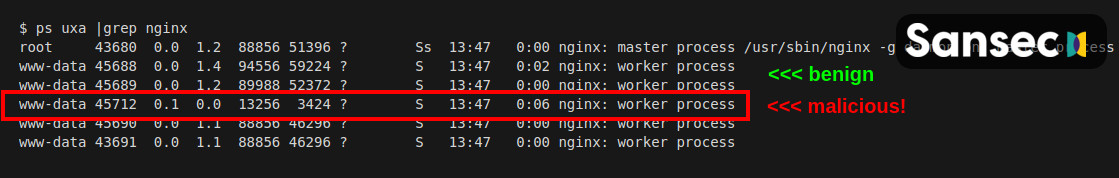
At the end of the procedure, the Nginx method embeds the distant accessibility malware in a way that can make it virtually extremely hard to inform apart from a legitimate process.
In a complex report these days, Sansec explains that NginRAT lands on a compromised method with the help of CronRAT through the custom “dwn” command that downloads the malicious Linux process library to the “/dev/shm/php-shared” area.
The library is then released making use of the LD_PRELOAD debugging aspect in Linux that is usually employed to take a look at process libraries.
Very likely to mask the execution, the risk actor also extra the “help” alternative numerous instances at the stop. Executing the command injects the NginRAT into the host Nginx app.
Since NginRAT hides as a regular Nginx process and the code exists only in the server’s memory, detecting it may well be a obstacle.
Nonetheless, the malware is launched employing two variables, LD_PRELOAD and LD_L1BRARY_Route. Directors can use the latter, which contains the “typo,” to expose the lively destructive procedures by operating the subsequent command:
$ sudo grep -al LD_L1BRARY_Path /proc/*/approximativement | grep -v self/
/proc/17199/environ
/proc/25074/environSansec notes that if NginRAT is discovered on the server, directors really should also check out the cron jobs because it is really probably that malware is hiding there, far too, extra by CronRAT.










More Stories
How Fairfield-based Knocking became CT’s fastest-growing startup
Amazon will start out tests drones for treatment deliveries
AI Briefing: Klarna hopes visual research in its e-commerce platform will assistance shoppers bridge in-man or woman, electronic hole